Risk Management:
Policies and Risks
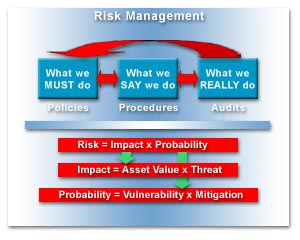
Risk
management is the top level of Information
Security - without knowing what threats we
face or what we are trying to protect or the
priority of the assets, there is really no
need or justification to invest time or
money in technologies that will protect
assets or mitigate against threats.
Defining
the Rules - Policies:
First we must
figure out what is business critical to us
and then define security policies that on a
strategic level defines how we ensure the
organisation will continue to exist or grow.
This includes identifying critical assets or
services that must be protected for business
continuity and identifying risks that may
impact or totally destroy the business.
• Policies are what we define we MUST
do to ensure business continuity.
With security
policies defined we can start determining
how we will implement these policies and
uphold the requirements with controls. We
must define the procedures that should be
followed to ensure implementation that is
alligned with the policies.
• Procedures are what we SAY we do to
ensure business continuity.
Finally we
need to make sure the policies and
procedures are followed and actually can be followed.
This is done by audits that verifies what is
actually being done and checks if this is in
allignment with both policies and procedures.
If there are things that are not alligned,
we must determine why and perform corrective
actions, either stronger enforcement or
implement changes to policies or procedures
that may be impossible to follow.
• Audits are done to verify what we
REALLY do and to perform corrective actions
if policies and procedures are not followed.
Risk is about Cost and Vulnerability:
In essence,
Information Security practise and
investments are made to make nothing happen.
This makes it hard to prove that the
technology and work done has a positive
value. We need to show what the cost would
be if we did nothing and something did
happen - what it would cost to live with a
threat as it is?
It could be cost of damage, burden
on support staff, loss of customers or loss
of revenue - all these are possible outcomes
if a threat is not mitigated or eliminated.
We can accept to live with a threat (cost
benefit analysis), we can mitigate a threat,
we can transfer a threat (e.g. insurance,
outsource the the public website) or we can
ignore a threat (hoping we wont be exposed
or attacked).
What a company will do must be based on the
security policies and will be dictated by
the financial capabilities. Other things may
also have impact, e.g. lack of resources,
lack of qualified personel, past experience,
company profile,
etc.
So the only justifiable way to get
initiatives funded in a corporation
environment is and should be by
demonstrating what the Risk is. This
includes
determining the impact of threats and the
probabilties that the threats will occur.
• Risk = Impact
x Probability
Please notice
that Risk is a cost value! So when we
suggest a security investment to mitigate a
risk we can and should be able to see a
reduction of the overall Risk value - if not
the investment is not worth it.
The Impact
of each threat is calculated by the value of
an asset or service multiplied by the
threats impact on the asset or service.
• Impact = Asset Value x Threat
The
probability of a threat to happen is based
on the vulnerability of our assets, services
or systems and the mitigations we have put
in place to limit or prevent these
vulnerabilities. Vulnerability will depend
on exposure, software errors and bugs, the
attacker population and if the organisation
is a high profile target, e.g. by having
valuable assets or reputation.
• Probability = Vulnerability x
Mitigation
So the final
formula for calculating the risk for each
threat is:
Risk =
Asset Value x Threat x
Vulnerability x Mitigation
Now that we
know the current ALE (annual loss
expectency) value, we can look at ways to
minimize any or more of the components, e.g.
decrease threat impact on an asset, remove a
vulnerability or implement better ways to
mitigate the threat.
Vulnerability Trees and Threat Analysis:
Before we can
select the appropriate actions and
investments to take to mitigate a threat,
remove vulnerabilities or minimize impact of
a threat, we must analyze what we are up
against. An internal study inside Microsoft
shows that if we look at motive and skill
level of the attackers, we can
categorize the attackers in groups and
related costs/volume/growth.
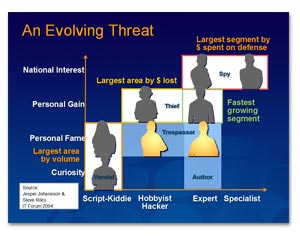
As can be
seen in the picture to the left (click to
enlarge), the largest
area of volume is the attacks that requires
little or no skills to perform against known
vulnerabilities. Even though this low
hanging fruit may not cost much per incident
the raw volume and easy mitigation must make
it the first priority, implemented in the
core Defense In Depth strategy.
Based on the
company, industry, regulatory compliance and
competition, we must evaluate where the
money are best spend. As a start, a Pareto
Principle (80/20) approach might be a good
starting point (especially if no formal
security function exists in the
organisation). This way we could identify
the critical 20% of our assets that makes
80% of our revenue and begin with a proper
protection of these assets. We can also look
at the 20% most dominant threats that causes
80% of the security breaches, e.g. looking
at SANS' statistics, and then implement
mitigation for these threats. In the end,
this is just a simple Risk Management model,
but it will go far for the small businesses.
Finally, we
can make a proper Risk Management
assessment, where we perform a detailed
analysis of all assets, threats and
vulnerabilities.
There is generally 3 ways
to handle Risk Management assessments, firstly purely
based on quantitative values, secondly based on
qualitative values only and finally a mixture of both
quantitative and qualitative values. The method used
will mostly be based upon your assets complexity,
critical business value and time retraints. The
quantitative method is very detailed and accurate but
time consuming, whereas the qualitative method is less
detailed and faster. The mixture tries to use the best
of both worlds.
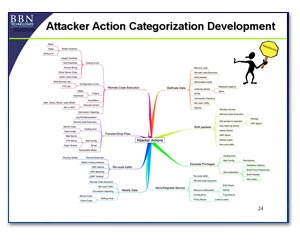 To evaluate
vulnerabilities, we can draw a Vulnerability
Tree or make a Threat Model. The image to
the left is from John Lowry's presentation
at the Digital Forensic Reseach Workshop
August 2004 (click to enlarge). It shows a
generic vulnerability tree that can be used,
but you must be aware that it was never ment
to be complete and has not been updated
since 2004.
To evaluate
vulnerabilities, we can draw a Vulnerability
Tree or make a Threat Model. The image to
the left is from John Lowry's presentation
at the Digital Forensic Reseach Workshop
August 2004 (click to enlarge). It shows a
generic vulnerability tree that can be used,
but you must be aware that it was never ment
to be complete and has not been updated
since 2004.
•
John Lowry's
presentation at the Digital Forensic
Research Workshop 2004
To make a
more current and relevant Vulnerability Tree
or a Threat Model, you can begin by looking
at your implemented Defense In Depth
mitigations, your assets and infrastructure,
as well as your behaviors. The basics of
Security is CIA - Confidentiality, Integrity
and Availability, so how can an attacker
break any of those for all your mitigations
in DiD, for your assets and infrastructure,
and the way your company and employees
behave (e.g. telecommuting, dialin, etc.)?
In the end
this task is pretty hard and requires staff
with a lot of technical knowledge - both in
the IT technology area as well as in the IT
Security field - and they must keep
themselves informed on the latest tools,
techniques and exploits. The sad thing is that it is
also
hard to get straight answers from anyone -
even the vendors!
Let us list a
few we have pondered about, still without
answers:
- Can an
attacker get the offline data on a
Windows Mobile 5 device without cracking
either the username/password or cracking
the offline data by bruteforce?
- Is the
exchange settings storing the domain
credentials in clear text easy
accessable on a Windows Mobile 5 device?
- How hard
is it to extract data from a mobile
device, e.g. Cell phone or PDA?
- How hard
is it really to piggy bag into a
corporate network if the user has a
connection to other networks (e.g. the
Internet) at the same
time a VPN is running (split tunneling)?
Continued Effort:
By performing
the above actions does nowhere mean that the
job is done. This is a continuing effort and
should be done on a regular basis where one
reviews the Policies and Procedures,
re-evaluates the Risks and changes to the
environment, as well as reviews the
implemented Defense in Depth plan.
More
Information:
See more on
Risk Management concepts here:

